Crime that involves a computer and a network, where the computer may have been a target or may have been used to commission the crime. It may threaten a person or nation’s security and financial health. Cybercrime crossing national borders and involving a crime committed by at least one nation-state is referred to as cyber warfare. Most, but not all, cybercrime is completed by profit-driven cybercriminals or hackers. Individuals or groups can commit cybercrime. Some cybercriminals are well-organized, employ advanced strategies, and have a high level of technical expertise. Others are newcomers to hacking. These could be either political or personal in nature. Examples: Identity theft, human and drug trafficking, hacking, etc.
In the beginning of 1970s, crimes over telephones were committed. The first person to be convicted of cybercrime was Ian Murphy, also known as Captain Zap, in 1981. He hacked the American telephone company to manipulate their internal clock, so that users could make free calls at peak times. The first cyber criminal in India, Amit Tiwari had been on the watch list since 2003 until he was finally caught in 2011.
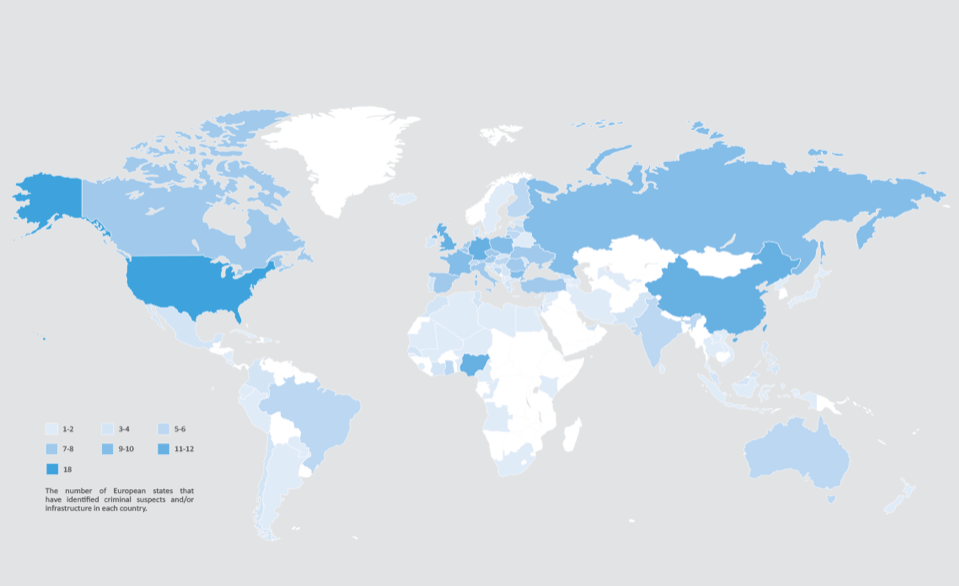
The country with the highest rate of cyber crime is USA (23.9%) followed by China (9.63%) .
CATEGORIES OF CYBERCRIME
- The attack is directed towards a computer, such as a data breach on a corporate network.
- A computer is used as a weapon in an attack, such as a denial of service (DoS) attack.
- A computer is a tool used in the commission of a crime, such as digital identity theft, which leads to the theft of funds from a bank account.
TYPES OF CYBERCRIME
- Financial Fraud: Dishonest misinterpretation of a fact intended to let another do or refrain from doing something that causes loss. Example: Fake e-mails
- Online Harassment /Cyber Bullying/ Internet Trolls: Misusing personal information or passing derogatory comments at specific individuals of a race, gender, colour, etc.
- Hacking: hacking is unauthorised access into a computer system and/or network.Because of the public coverage, government websites are a popular target for hackers. Hackers appreciate the media attention. The motivation for hacking is greed, power, publicity, revenge, adventure and the desire to access restricted information. Shutting down or misusing websites or computer networks.
- Defamation: It involves any person with intent to lower down the dignity of the person by hacking his mail account and sending some mails with using vulgar language to unknown persons mail account.
- Cyber Terrorism: Politically motivated use of computers and IT to cause serious disruption and fear in society. Terrorist attacks on the Internet is by distributed denial of service attacks, hate websites and hate E-mails, attacks on service network etc.
- Child Pornography: In this cyber crime defaulters create, distribute, or access materials that sexually exploit underage children.
- Virus Dissemination: Malicious malware that infects other programmes. Examples: Web Jacking, email bombing, Virus, Worms, Trojan Horse, Web Jacking etc.
- Computer Vandalism: Cyber vandalism is the act of damaging or destroying data rather than stealing or misusing it. This is a type of programme that attaches itself to a file and then circulates it.
PREVENTION
- It is best not to give out personal information to strangers via e-mail, chat, or other social networking sites.
- Avoid transmitting any photograph to strangers through the internet, as incidences of photograph misuse or modification are on the rise.
- All netizens should use up-to-date anti-virus software to protect themselves from virus attacks.
- To avoid fraud, a person should never send credit card or debit card details to an un-secure website.
- Using strong passwords for different account can help in prevention.
- Managing social media settings as we have different private social media setting so that no one can see our private information.
- Using a full time internet and overall security software.
- Practicing safe web surfing.

You must be logged in to post a comment.