Citation
Lariosa, Z., & Junio, O. (2026). Development of an Arduino-Based Smart Security System Integrating User Type, Authentication Method, and Access Status for Enhanced Access Control. International Journal of Research, 13(4), 189–196. https://doi.org/10.26643/ijr/edupub/19
Zandrex Lariosa, Oliver Junio
c1-241-02102@uphsl.edu.ph, omj@uphsl.edu.ph
University of Perpetual Help System Laguna
Abstract
The increasing trend of hacking attacks and security violations in addition to inefficiencies in access control mechanisms is one reason that calls for the implementation of an intelligent security mechanism. The purpose of this research is to design and implement the Arduino-based intelligent access control security system, which considers user type, authentication method sequence, and access status to strengthen multi-level access controls. With regards to the DiD security layer concept, the ABAC principle, and the IPO framework, the system features RFID and fingerprint-based sequential authentication to enhance the security process.
The designed system entails the use of RFID and fingerprint technology, attendance logging in real-time, intrusion detection, sending of alerts through email and SMS messages, remote monitoring via the Internet, and analysis of access pattern based on time and frequency of access. For this study, the descriptive developmental method of research was utilized, along with a waterfall software development process. The evaluation of the software was conducted among small business owners and IT personnel residing in the City of Trece Martires, Cavite, using the ISO/IEC 25010 software quality framework.
The results revealed that the proposed system is highly acceptable and efficient as a cost-effective smart security system. The inclusion of multi-factor authentication, real-time monitoring, and intelligent access control analysis improved the reliability of the security and access control system process. This study has contributed to the existing literature on Arduino and IoT security systems in that it demonstrated the practicality of implementing multi-factor authentication, role management, and intelligent monitoring into small business settings.
Introduction
The rapid advancement of technology has led to a corresponding increase in security threats, particularly in small businesses where resources for advanced protection are limited. Traditional access control systems, which often rely on single authentication methods, are becoming inadequate in addressing modern challenges such as unauthorized access, theft, and data breaches. These systems lack flexibility, real-time monitoring, and adaptive capabilities, making them vulnerable to exploitation. While previous studies have explored the use of RFID, biometrics, and monitoring technologies, many remain limited to isolated implementations without integrating multiple security layers or intelligent analysis.
To address these limitations, this study proposes the development of an Arduino-based smart security system that integrates multi-layered authentication mechanisms. The system utilizes a sequential process where RFID verification is followed by fingerprint authentication, ensuring enhanced identity validation before granting access. It also incorporates role-based access control for different user types and provides real-time monitoring of system activities, including detection of unauthorized access and intrusion attempts. This structured approach strengthens security by combining multiple authentication methods and improving overall access control efficiency.
In addition, the system introduces an intelligent access behavior analysis component that evaluates user activity based on time patterns and frequency of access attempts. This enables the detection of unusual or suspicious behavior, contributing to proactive security management. Designed as a cost-effective and open-source solution, the system is suitable for small businesses, offices, and similar environments. Overall, the study contributes to the development of a scalable and efficient smart security system that integrates multi-factor authentication, user management, and intelligent monitoring to address the limitations of existing access control technologies.
METHODOLOGY
This study employed a descriptive-developmental research design combined with the Waterfall software development model to design, develop, and evaluate an Arduino-based smart security system. The approach enabled the researchers to first assess existing security practices among small businesses, identify system requirements, and subsequently develop a solution that addresses identified gaps. The methodology followed a structured process consisting of needs assessment, system development, and evaluation, ensuring that the resulting system is both technically sound and aligned with user needs.
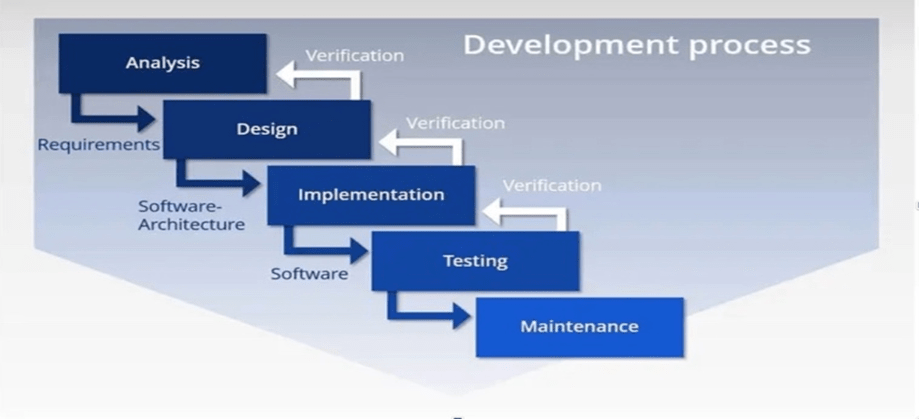
The system development process followed the Waterfall model, which consists of sequential phases: analysis, design, implementation, testing, and maintenance. During the analysis phase, system requirements and security challenges were identified. The design phase involved planning the hardware and software architecture, including the integration of RFID, fingerprint sensors, and web-based monitoring. Implementation focused on coding and assembling the hardware components, while testing ensured system accuracy, reliability, and performance. The Waterfall diagram is included in this study to illustrate the step-by-step development process followed.
The architecture of the system integrates both hardware and software components to support a multi-layered security mechanism. The system utilizes RFID and fingerprint authentication, a microcontroller (Arduino/ESP32), a web-based platform, and notification systems for real-time alerts. It enables role-based access control for administrators and staff, attendance monitoring, and intrusion detection based on unauthorized access attempts or irregular usage patterns. The design ensures secure, efficient, and reliable access control supported by real-time monitoring capabilities.
Data for system evaluation were collected from 100 purposively selected respondents, including business owners, staff, and IT professionals from Trece Martires City, Cavite. A structured questionnaire based on the ISO/IEC 25010 software quality model was used to assess system performance across nine criteria, including functionality, efficiency, security, and reliability. Data gathering procedures included surveys, usability testing, and interviews, while analysis was conducted using weighted mean and Likert scale interpretation. Ethical standards such as informed consent, confidentiality, and voluntary participation were strictly observed throughout the study.
Results and Discussion
The results of the study revealed that most small businesses still rely on traditional security mechanisms such as manual locks and basic surveillance systems, which are often not actively monitored and lack real-time alert capabilities. These systems are vulnerable to unauthorized access and fail to provide immediate response during security breaches. The findings highlight the need for a more advanced and integrated security solution that addresses these limitations through automation and multi-layered protection.
Based on the identified needs, the proposed Arduino-based smart security system was designed to incorporate key features such as multi-factor authentication using RFID and fingerprint scanning, real-time monitoring, attendance tracking, and remote access via a web-based platform. The system also includes alert mechanisms that notify administrators through SMS and email in cases of unauthorized access. These features directly respond to the operational requirements of small business owners and staff, improving both security and administrative efficiency.
The evaluation results showed that the system achieved “Excellent” ratings across all software quality attributes based on the ISO/IEC 25010 framework. IT experts, business owners, and staff consistently rated the system highly in terms of functional suitability, performance efficiency, compatibility, interaction capability, reliability, security, maintainability, flexibility, and safety. Among these, security received the highest ratings, indicating strong confidence in the system’s ability to protect against unauthorized access. Slightly lower but still excellent ratings in interaction capability suggest opportunities for further improving user interface design.
Overall, the findings demonstrate that the developed system is highly acceptable, reliable, and effective for small business environments. The integration of multi-layered authentication, real-time monitoring, and intelligent alert mechanisms significantly enhances security operations compared to traditional systems. The results also confirm that the system is practical, user-friendly, and adaptable, making it a viable solution for improving access control and security management in small-scale enterprises.
| Criteria | IT Experts | Employers | Staff | Overall Mean | Interpretation |
| Functional Suitability | 4.83 | 4.53 | — | 4.68 | Excellent |
| Performance Efficiency | 4.80 | 4.33 | — | 4.57 | Excellent |
| Interaction Capability | 4.73 | 4.30 | — | 4.52 | Excellent |
| Compatibility | 4.85 | 4.55 | — | 4.70 | Excellent |
| Reliability | 4.80 | — | 4.46 | 4.63 | Excellent |
| Security | 4.92 | 4.64 | — | 4.78 | Excellent |
| Maintainability | 4.84 | — | 4.56 | 4.70 | Excellent |
| Flexibility | 4.70 | — | 4.59 | 4.65 | Excellent |
| Safety | 4.80 | — | — | 4.80 | Excellent |
The statistical results indicate that the developed Arduino-based smart security system achieved consistently high ratings across all nine ISO/IEC 25010 software quality characteristics, with all computed means falling within the “Excellent” range (4.20–5.00). The overall grand mean of 4.67 confirms a very high level of acceptability and performance among all respondent groups, including IT experts, employers, and staff.
Among the evaluated criteria, Security (4.78) obtained the highest overall mean, reflecting strong confidence in the system’s ability to prevent unauthorized access and ensure data protection. This is followed by Compatibility and Maintainability (4.70), indicating that the system is adaptable across different environments and easy to manage. These findings suggest that the integration of multi-layered authentication and real-time monitoring significantly enhanced system robustness.
On the other hand, Interaction Capability (4.52) received the lowest mean, although it still falls under the “Excellent” category. This implies that while users find the system highly functional and reliable, there is still room for improvement in terms of user interface design and ease of interaction, particularly for non-technical users.
Overall, the statistical findings validate that the system is highly reliable, efficient, secure, and user-acceptable, making it a viable solution for improving access control and security management in small business environments.
Conclusion
This study concludes that Chinese technology enterprises demonstrate a high level of effectiveness in contract management practices, supported by well-established governance frameworks and positive contractor relationships; however, these practices do not directly translate into enhanced contractor performance. While effective contract management significantly improves relationship quality, contractor performance appears to be influenced by additional factors such as innovation capability, technological competence, and performance-based incentives. This indicates that contract management, while essential, must be strategically integrated with performance monitoring mechanisms and outcome-driven evaluation systems to generate measurable improvements. Therefore, to maximize contractor performance, technology enterprises must move beyond compliance to adopt performance-oriented contracting models that promote accountability, innovation, and continuous improvement.
Recommendations
Based on the findings of the study, several recommendations are proposed to further enhance the functionality, security, and usability of the developed system. First, the development of a mobile application is recommended to allow remote monitoring of access logs, user management, and real-time alert notifications. This will significantly improve user interaction, accessibility, and convenience, especially for administrators who need to manage the system off-site. In addition, the implementation of data encryption and secure communication protocols is strongly suggested to strengthen data protection, ensuring that sensitive information is safeguarded against potential data breaches and unauthorized access.
Furthermore, the inclusion of a device expansion module is recommended to improve system scalability. This feature may integrate an access point (AP) hotspot capability, enabling users to easily connect to Wi-Fi and manage multiple devices across different business branches efficiently. Another important enhancement is the incorporation of an emergency key mechanism, which can be used to grant access during unexpected situations such as power outages or internet interruptions, ensuring continuous system functionality.
Finally, the system can be further upgraded by incorporating advanced multi-factor authentication mechanisms that combine RFID technology, fingerprint scanning, and AI-based access behavior analysis. This enhancement will provide an additional layer of security by not only verifying user identity but also assessing access patterns for potential anomalies. Overall, these recommendations aim to improve the system’s adaptability, security, and reliability, making it more robust and suitable for wider implementation in various business environments.
References:
Afreen H., Kashif M., Shaheen Q., Alfaifi Y. H., & Ayaz M. (2023). IoT-Based Smart Surveillance System for High-Security Areas. Applied Sciences, Volume 13 Issue 15, 8936. https://doi.org/10.3390/app13158936
Alaba, A. F., Othman, M., & Hahsem, I. A. T. (2017). Internet of things security: A survey. Journal of Network and Computer Applications 88. https://doi.org/10.1016/j.jnca.2017.04.002
Ameer, S., Benson, J., & Sandhu, R. (2022). An Attribute-Based Approach toward a Secured Smart-Home IoT Access Control and a Comparison with a Role-Based Approach. Information 2022, 13(2), 60; https://doi.org/10.3390/info13020060
Atif Afroz (2022). Digital Smart Door Lock Security System Using Arduino Uno Microcontroller. Iconic Research and Engineering. JUL 2022, IRE Journals, Volume 6 Issue 1, ISSN: 2456-8880
Badmus E.O, Odekunle O.P, & Oyewobi D.O (2021). Smart Fingerprint Biometric and RFID Time-Based Attendance Management System. European Journal of Electrical Engineering and Computer Science. 5, 4 (Jul. 2021), 34–39. DOI: https://doi.org/10.24018/ejece.2021.5.4.339.
Bhanushali M., Bhanushali D., Chaugule A., & Bhelande M. (2020). Biometric Authentication System using Arduino. Journal of Advancement in Parallel Computing, 3(3), 1–5. https://doi.org/10.5281/zenodo.4335458.
Bounabi B., Mosbah C., Khiter O., & Soussi Y. (2024). Design and implementation of an intelligent building security system using Arduino GIGA R1 Wi-Fi. Vol. 5 No. 2 (2024): Studies in Engineering and Exact Sciences, Curitiba, v.5, n.2, 2024. https://doi.org/10.54021/seesv5n2-217
Irugalbandara, C., Naseem, A. S., Perera, S., Kiruthikan, S., & Logeeshan, V. (2023). A Secure And Smart Home Automation System With Speech Recognition And Power Measurement Capabilities. Sensors, 23(13), 5784.
Kassim, S.O, Idriss, A.S, Ahmed, A.I, (2023). Implementation of a Sustainable Security Architecture Using Radio Frequency Identification (RFID) Technology for Access Control. https://doi.org/10.48550/arXiv.2304.04628
Khabarlak K. & Koriashkina L. (2021). Mobile Access Control System Based on RFID Tags and Facial Information. In Bulletin of National Technical University “KhPI”. Series: System Analysis, Control and Information Technologies 2 (4) (2020): 69-74. https://doi.org/10.20998/2079-0023.2020.02.12
Kordov K. & Bilyal I. (2023). Access Control System Using Arduino Microcontroller and RFID Reader. Annual of Konstantin Preslavsky University of Shumen Faculty of mathematics and informatics XXIV C:9-15, https://doi.org/10.46687/QSFY7970
Lavanya Y., Rajitha Laksjmi M., Tarun V., Suma P., & Rakesh P. (2024). Design and Development of Biometric and Keypad Based Smart Door Security System for Residential Building. Vol. 10 No. 3: IJERAT May-2024. https://doi.org/10.31695/IJERAT.2024.3.2
Mohammed M. Sultan, Amer T. Saeed, & Ahmed M. Sana (2021). Design and implementation of an adaptive multilevel wireless security system using IoT. Vol.23, No.3 Institute of Advanced Engineering and Science (IAES). http://doi.org/10.11591/ijeecs.v23.i3.pp1804-1813
Mumtaz Z., Ilyas Z., Sohaib A., Ullah S., & Madni H.A. (2020). Design and Implementation of User-Friendly and Low-Cost Multiple-Application System for Smart City Using Microcontrollers. https://doi.org/10.48550/arXiv.2010.07016
Pamarthy, S. K. (2025). AI-Powered Risk-Based Access Control: Advanced Security Framework For Modern Systems. International Journal Of Research In Computer Applications And Information Technology, 8(1), 3031–3045.
Shreehari H S., Vinolya S, Siriguppa & Varshitha (2022). Smart Attendance System based on Biometrics and Location’s Boundary Conditions. (IJERT) ICEI – 2022 (Volume 10 – Issue 11), DOI : 10.17577/IJERTCONV10IS11024
Singh, J., Rani, S., & Kumar, V. (2024). Role-Based Access Control (RBAC) enabled secure and efficient data processing framework for IoT networks. International Journal of Communication Networks and Information Security, 16(2), 19–32.
Shubham R., Avinash G., Mudaliyar R. & Pratiksha P. (2020). Industry based security system using GSM and Arduino. Volume 5 Issue 3 March 2020 ISSN (Online) 2456-0774.
Sujatha, M., Muthusamy, M., Surya, T., Ravi, K., & Reddy K. (2022). Door locking system with Arduino based on mobile authentication. IP Conference Proceedings. 2022, Vol. 2452 Issue 1, p1-10. 10p. AIP Conf. Proc. 2452, 070002 (2022). https://doi.org/10.1063/5.0118165
Vinodhini S., Gnanavarshini S., Sheryl E., & Divya Prapanjani PA. (2024). Password based Smart Doorlock System using Arduino UNO for Enhanced Security. IRO Journal on Sustainable Wireless Systems Volume 6, No. 2 (2024): 95-109. http://doi.org/10.36548/jsws.2024.2.002
Zhou, W., Jia, Y., Yao, Y., Zhu, L., Guan, L., Mao, Y., Liu, P., & Zhang, Y. (2018). Discovering and understanding the security hazards in the interactions between IoT devices, mobile apps, and clouds on smart home platforms. arXiv. arXiv:1811.03241.


You must be logged in to post a comment.